The 2026 Synthetic Identity Crisis:
The New Credit Apocalypse
Published: April 24, 2026 | Estimated Reading Time: 65 minutes | Part of the ScorePivot Identity Protection Series
Synthetic identity fraud grew eightfold in 2025, now comprising 11% of all global fraud. Your credit file may already be compromised without any alert, notification, or visible sign on your credit report.
This is the cornerstone resource in the ScorePivot Identity Protection Series. Bookmark this page. Share it. Return to it. This is the guide you will wish you had before your credit file was compromised. Twenty sections. Seventy data points. One protocol that could save your financial identity.
Why This Matters Right Now
If you have a Social Security number, you are a potential component in someone else's fabricated identity. The LexisNexis 2026 Cybercrime Report documents an 800% year-over-year increase in synthetic identity fraud. The Federal Reserve estimates $35 billion in losses from this crime in 2023 alone. AI-enabled fraud losses are projected to reach $40 billion by 2027.
Independent review. We may earn a referral, but your price stays the same.
Section 1: Why Your Credit File May Already Be Compromised
Synthetic identity fraud grew eightfold in 2025, now comprising 11% of all global fraud, according to the LexisNexis 2026 Cybercrime Report. Unlike traditional identity theft, synthetic fraud creates entirely new "people" using fragments of your real data — meaning your credit file may be compromised without any alert, notification, or visible sign on your credit report. If you have a Social Security number, you are a potential component in someone else's fabricated identity.
Picture this. It is a Tuesday morning. You sit down at your kitchen table with a cup of coffee and open your laptop to check your credit report. You have done everything right. You have paid every bill on time for twenty years. You have never missed a mortgage payment. Your credit cards carry modest balances. You are, by every traditional measure, a model borrower. And yet, something is wrong.
There is an address on your Experian report you have never lived at — a mail drop in a strip mall two states away. There is an inquiry from an auto lender you have never contacted. There is an authorized user account on a credit card you have never seen. Your stomach drops. You have been hacked, you think. Someone stole your identity.
But here is the twist that makes 2026 different from every year that came before it. No one stole your identity. Not in the way you understand the word "steal." Someone built a new person using pieces of yours. They took your Social Security number — just the number, not your name, not your date of birth, not your mother's maiden name — and they attached it to a fabricated name, a generated date of birth, an AI-produced photograph that looks like a real human being but is not. They created a synthetic identity. A ghost. A person who has never existed, who has never breathed, who has never signed a lease or shaken a hand. And that ghost has been building credit for the last eighteen months using your SSN as its foundation.
This is not a hypothetical scenario. This is the mathematical reality of the year 2026. According to the LexisNexis Risk Solutions 2026 Cybercrime Report — which analyzed more than 116 billion online transactions processed through the LexisNexis Digital Identity Network — synthetic identity fraud exploded eightfold year over year in 2025. It now comprises 11% of all reported fraud globally, making it the single fastest-growing fraud type on the planet. Not credit card skimming. Not phishing. Not account takeover. Synthetic identity fraud. The creation of people who do not exist, built on the data of people who do.
2026 Synthetic Identity Fraud by the Numbers
8x
Year-over-year growth in 2025
11%
Of all global fraud
$35B
Federal Reserve estimated losses (2023)
$40B
Projected AI-enabled fraud losses by 2027
The scale of this problem defies casual comprehension. The Federal Reserve has identified synthetic identity fraud as "the fastest-growing type of financial crime in the United States." The Federal Reserve's Synthetic Identity Fraud Mitigation Toolkit estimates that synthetic identity fraud caused losses of approximately $35 billion in 2023 alone. Industry projections tracked by Help Net Security and the Business Information Industry Association (BIIA) place AI-enabled fraud losses on track to reach $40 billion by 2027.
CaraComp's 2026 analysis reveals a particularly disturbing ratio: synthetic identities account for just 4% of all fraud cases — but they generate 7% of total financial losses. This is not a volume crime. This is a severity crime. Every synthetic that detonates leaves a crater far deeper than the average fraud event.
What makes this fraud category uniquely terrifying is its invisibility. Traditional identity theft has a victim who knows they are a victim. Your credit card gets cloned, you see charges you did not make, you call your bank, you file a dispute. There is friction. There is detection. There is a human being who sounds the alarm. Synthetic identity fraud has no such mechanism. The "person" who opened those accounts is not you. It is a ghost wearing your SSN like a mask. The ghost pays its bills. It looks like a responsible borrower. The credit bureau has no reason to question the file. The lender has no reason to flag the account. And you — the real person whose SSN anchors the entire scheme — have no way to see the parallel file that the ghost has been cultivating in the shadows.
Primary Targets: Who Is Most Vulnerable
- Children: Their SSNs are clean — no credit history, no monitoring, no alerts. A child's SSN can be harvested and used undetected for 15-18 years until they apply for their first credit.
- Elderly individuals: Populations least likely to be actively monitoring their credit files, with longer existing credit histories available for piggybacking schemes.
- Deceased persons: SSNs remain in circulation long after death, and the Death Master File is not updated in real-time or universally checked by lenders.
If you have a Social Security number, you are a potential component in someone else's synthetic identity. That is not hyperbole. That is not a marketing scare tactic. That is the mathematical reality of 2026, when 11% of all global fraud involves fabricated identities stitched together from real data belonging to real people who have no idea they have been incorporated into a criminal enterprise.
CTA #1: Scan Your Credit for Synthetic Contamination
The ScorePivot Synthetic Identity Risk Scanner checks for 47 indicators of synthetic contamination. Free. 90 seconds. Know where you stand.
Run Your Free Scan NowIndependent review. We may earn a referral, but your price stays the same.
This content is for educational purposes only and does not constitute legal, financial, or credit repair advice. ScorePivot is not a credit repair organization and does not provide credit repair services. Consult a qualified professional before making financial decisions.
Section 2: The Anatomy of a Synthetic Identity — How Criminals Build People Who Do Not Exist
Criminals create synthetic identities through a six-phase lifecycle: SSN harvesting from data breaches or vulnerable populations, identity assembly using fabricated names combined with real SSNs, credit file seeding through denied applications that create inquiry records, piggybacking on real accounts to inherit credit history, an incubation period of 6 to 24 months building a pristine profile, and finally a "bust-out" where every credit line is maxed simultaneously before the synthetic persona vanishes permanently.
To understand how to defend against synthetic identity fraud, you must first understand how it works. Not in vague, general terms. In precise, operational detail. Because the sophistication of the attack is what makes it so difficult to detect, and the difficulty of detection is what makes it so devastatingly effective. The synthetic identity lifecycle operates in six distinct phases, each building on the last, each designed to exploit a specific weakness in the financial system's architecture.
Phase 1: SSN Harvesting
Every synthetic identity begins with a real Social Security number. The number is the anchor. SSNs are harvested from multiple sources. The dark web remains the primary marketplace — following major data breaches at organizations like Equifax (2017, 147 million records), T-Mobile, Capital One, and countless others, billions of SSNs are circulating in underground markets. A single SSN with no associated credit history — typically belonging to a child, elderly person, or recently deceased individual — can be purchased for as little as one to five dollars. The supply is effectively infinite.
Phase 2: Identity Assembly
With a harvested SSN in hand, the fraudster constructs a complete identity profile. This is where generative AI has transformed the game. The fabricated name is generated to sound plausible. The date of birth is chosen strategically — typically placing the synthetic in the 25-to-45 age range. An AI-generated photograph is produced using deepfake technology. Graphika documented over 50 cases of deepfake financial scams across YouTube, TikTok, and Facebook in March 2026 alone. A burner phone number provides contact. A mail drop provides address. The result is a complete identity dossier for a human being who has never existed.
Phase 3: Credit File Seeding
This is the phase that exploits the fundamental design of the credit reporting system. The synthetic identity applies for credit — typically a credit card or small personal loan. The application is almost always denied. But here is the critical mechanism: the denial itself creates a record. When the lender submits the application to the credit bureau, the bureau searches for a matching file. It finds the SSN but does not find a matching name. Depending on the bureau's matching algorithm, it may create a new credit file. The inquiry is logged. The file is seeded. A ghost has been born inside the credit reporting system.
Phase 4: Piggybacking and Authorized User Abuse
With a nascent credit file established, the synthetic identity needs to build credit history rapidly. The most efficient method is authorized user piggybacking. Fraud networks maintain portfolios of credit card accounts with long, pristine payment histories. The synthetic identity is added as an authorized user on one or more of these accounts. Under credit reporting rules, authorized users inherit the payment history and credit limit of the primary account. Overnight, a synthetic that had no history suddenly has years of on-time payments, high credit limits, and a utilization ratio that looks responsible.
Phase 5: The Incubation Period
This phase is what separates synthetic identity fraud from every other type of financial crime. It requires patience. The synthetic identity, now equipped with a credit file and some credit history, begins applying for its own credit products. These applications are often approved. The synthetic makes small purchases and pays every bill on time. It keeps balances low. It requests credit limit increases. Over a period of six to twenty-four months, the synthetic builds a pristine credit profile that is indistinguishable from that of a real, responsible borrower. Every fraud detection system is calibrated to flag suspicious behavior — the synthetic triggers none of these alarms.
Phase 6: The Bust-Out
After months or years of careful cultivation, the synthetic identity executes the final phase. Every credit line is maxed simultaneously. Cash advances are taken to the limit. Balance transfers are initiated. Purchases are made and immediately converted to cash or cryptocurrency. In the span of 48 to 72 hours, the synthetic extracts the maximum possible value — often totaling $50,000 to $200,000 or more per synthetic identity. Then the synthetic vanishes. The phone number is disconnected. The mail drop is abandoned. The AI-generated photograph belongs to no one. The lender discovers that the "person" who owes the debt does not exist. The debt is a total loss.
This six-phase lifecycle is not theoretical. It is operational. It is being executed at industrial scale by organized fraud networks around the world. And the person whose SSN anchors the entire scheme — the child, the retiree, the unsuspecting worker — may never know they were a part of it until the wreckage arrives at their doorstep years later.
Section 3: The 8x Explosion — Inside the LexisNexis 2026 Numbers
The LexisNexis Risk Solutions 2026 Cybercrime Report, analyzing 116 billion transactions through the Digital Identity Network, found that synthetic identity fraud grew eightfold year over year in 2025 and now represents 11% of all global fraud. First-party fraud remains the most common fraud type at 38.3% globally, but synthetic fraud is accelerating faster than any other category. Agentic AI bot traffic surged 450% across 2025, enabling fraud automation at unprecedented scale.
Numbers do not lie, but they can be overlooked. They can be buried in reports that most people never read, released in press announcements that most consumers never see. The LexisNexis Risk Solutions 2026 Cybercrime Report is one of the most important fraud intelligence documents published this year, and its findings should alarm every person with a credit file in the United States.
The report was derived from analysis of more than 116 billion online transactions detected through the LexisNexis Digital Identity Network in 2025. This is not a survey. This is not a projection based on a sample set. This is direct observational data from one of the largest transaction monitoring networks on the planet, encompassing financial services, e-commerce, communications, mobile and media, and gaming and gambling sectors across global markets.
LexisNexis 2026 Key Findings
- 8% rise in global fraud rates overall
- First-party fraud: 38.3% of all reported frauds (leading source for second consecutive year)
- Synthetic identity fraud: 11% globally — 800% year-over-year increase
- Latin America: Synthetic fraud at 48.3% of all reported fraud
- Agentic AI bot traffic: 450% surge across 2025
- Malicious bot attacks: 60% increase in 2025
- Login attacks: 89% increase
- Desktop browser attack rates: 100% increase (doubled)
Perhaps the most forward-looking finding in the report involves agentic AI. Traffic from AI-powered automated agents — bots that do not merely execute pre-programmed scripts but adapt, learn, probe defenses, and adjust their behavior in real time — surged 450% across 2025. Four hundred and fifty percent. This is not a gradual increase. This is an explosion.
The implications for synthetic identity fraud are direct and alarming. If a fraud network previously needed a team of humans to manually submit credit applications, build credit histories, and manage the incubation period for each synthetic identity, agentic AI now allows those processes to be automated at a scale that was previously unachievable. One operator with the right tools can now manage dozens, potentially hundreds, of synthetic identities simultaneously.
Meanwhile, the Graphika research unit documented 50 or more cases of deepfake financial scams across YouTube, TikTok, and Facebook in March 2026 alone. Twenty-seven accounts were found impersonating a single individual — Jaden Smith — for bank fraud purposes. The North Korean IT worker infiltration program continues to expand: ID.me suspended more than 130 digital wallets linked to DPRK operatives, with attempt volumes increasing 200%.
Stephen Topliss, Vice President of Fraud and Identity at LexisNexis Risk Solutions, stated that "cybercriminals are experimenting with the same technologies that are transforming digital commerce and organizations must prepare for a future where both legitimate users and malicious actors rely on automated agents to interact online." This is not a warning about the future. This is a description of the present.
Section 4: The $40 Billion Ghost — Why This Is the Fastest-Growing Fraud on Earth
Synthetic identity fraud is projected to contribute to $40 billion in AI-enabled fraud losses by 2027, with the Federal Reserve estimating $35 billion in losses in 2023 alone. The disproportionate severity — 4% of cases but 7% of losses — combined with the impossibility of recovering debts from nonexistent people makes synthetic fraud uniquely devastating to the financial system and ultimately to every legitimate borrower who pays the cost through higher rates and tighter lending standards.
Forty billion dollars. Let that number settle into your mind for a moment. Forty billion dollars is larger than the gross domestic product of over 90 countries. It is roughly the annual revenue of a Fortune 50 company. It is more than the combined budgets of the FBI, the Secret Service, and every federal law enforcement agency in the United States. And it is the projected scale of AI-enabled fraud losses by 2027 — a trajectory that synthetic identity fraud is accelerating faster than any other contributor.
To understand why synthetic fraud losses are so disproportionately large, you need to understand the economics of the bust-out. A traditional identity theft case has a ceiling on the damage. The criminal steals a real person's credit card, makes fraudulent charges, and the bank reverses them. The loss to the bank is typically a few hundred to a few thousand dollars per case.
A synthetic bust-out has none of these constraints. The synthetic identity has been cultivating credit for six to twenty-four months. It has accumulated multiple credit cards with $10,000, $20,000, $50,000 limits. It has a personal loan. Maybe an auto loan. When the bust-out happens, every line is maxed simultaneously. The total extraction from a single synthetic identity can range from $50,000 to $200,000 or more. And then the collection process begins — and the lender discovers that the debtor does not exist. There is no person to pursue. No wages to garnish. No assets to seize. The loss is total. One hundred cents on the dollar.
How Synthetic Fraud Costs YOU
- Higher interest rates: Lenders absorb billions in synthetic fraud losses and pass those costs to legitimate borrowers.
- Tighter lending standards: Borderline applicants are excluded due to increased default risk assumptions.
- Increased verification friction: Every legitimate credit application requires more documentation and longer wait times.
- Taxpayer burden: Synthetic identities defraud government benefit programs — unemployment, pandemic relief, tax refunds.
Government benefit programs are equally vulnerable. Synthetic identities have been used to claim unemployment benefits, pandemic relief funds, and tax refunds. The IRS, the Small Business Administration, and state unemployment agencies have all documented synthetic identity fraud targeting their programs. When these programs are defrauded, the cost is borne by taxpayers.
Auto lending is a particularly acute vulnerability. Synthetic identities with cultivated credit profiles can qualify for auto loans of $30,000, $40,000, or more. The vehicle is purchased, driven briefly, and then sold — often exported — while the loan goes into default. The National Insurance Crime Bureau has documented synthetic identity rings operating in the auto lending space with industrial efficiency.
The $40 billion number is not a scare tactic. It is a trajectory. Synthetic identity fraud is the fastest-growing fraud on Earth because it exploits the fundamental architecture of how identity, credit, and trust are structured in the modern financial system. And until that architecture is rebuilt, the losses will continue to compound.
Section 5: The Fragmented File Problem — When Your SSN Lives in Two Places
A fragmented credit file occurs when the same Social Security number is associated with two or more credit files at a bureau — typically one belonging to the real consumer and one belonging to a synthetic identity. This happens because credit bureau matching algorithms may create a new file when application data contains a known SSN but unfamiliar name and personal details. Fragmented files can cause legitimate consumers to be denied credit, have derogatory accounts appear on their reports, or face persistent mixed-file disputes that take months to resolve.
This is the technical heart of the synthetic identity crisis, and it is the mechanism through which the crime committed by a fabricated person becomes the problem of a real one. To understand fragmented files, you must first understand how credit bureaus build and maintain consumer records — because the vulnerability that synthetic fraud exploits is not a bug in the system. It is the system working exactly as it was designed to work, applied to a threat it was never designed to anticipate.
When a lender submits a credit application to a credit reporting agency — Equifax, Experian, or TransUnion — the bureau's matching algorithm attempts to link the application data to an existing consumer file. The algorithm uses multiple data points: Social Security number, name, date of birth, current address, previous addresses, and other identifying information. If the SSN, name, and date of birth closely match an existing file, the application data is appended to that file.
But what happens when the SSN matches an existing file but the name and other identifying details do not? This is the scenario that synthetic identities create. The bureau's algorithm encounters a paradox: the SSN matches your file, but the name, DOB, and address do not. The bureau may create a new file — a second file associated with the same SSN but under the synthetic's name.
Signs of Fragmented File Contamination
- Unknown addresses appearing on your credit report — addresses where you have never lived.
- Phantom inquiries from lenders you never contacted — indicating the synthetic applied for credit.
- Authorized user accounts you never authorized — piggybacking scheme leakage.
- Unexpected credit denials citing "insufficient credit history" or "derogatory accounts" that don't match your profile.
- Unfamiliar aliases in the "also known as" section of your personal information.
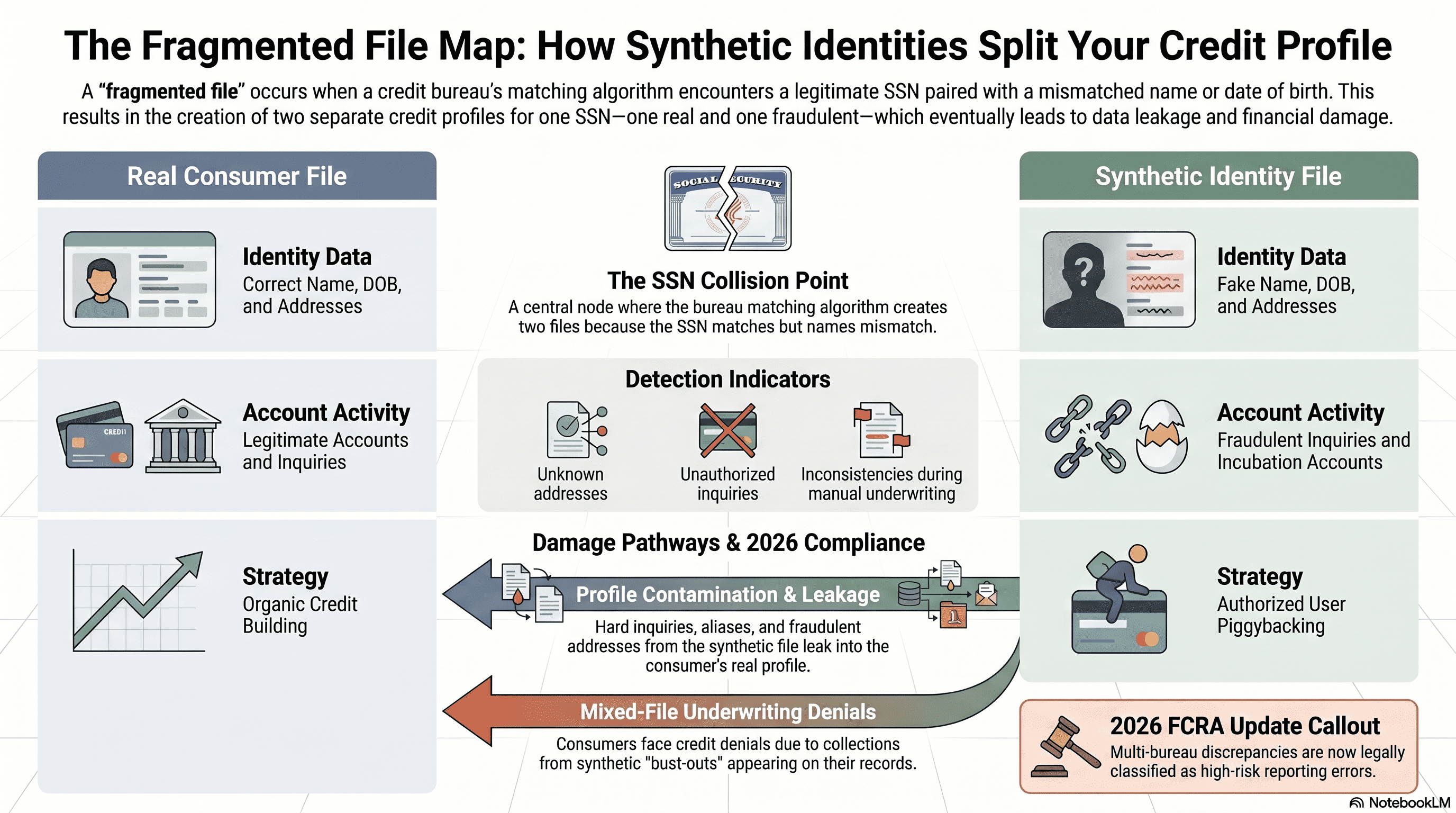
Infographic: How synthetic identities create fragmented credit files in 2026.
The 2026 FCRA updates have introduced a significant change that directly addresses fragmented files: multi-bureau discrepancies are now classified as "high-risk reporting errors." If the same consumer's data shows different account statuses, different balances, or different identifying information across Equifax, Experian, and TransUnion, that discrepancy now triggers priority review under the updated dispute process.
But the consumer must first know to look. Most consumers do not pull all three reports simultaneously and compare them line by line for discrepancies. They do not know what a fragmented file is. They do not know it is possible. And so the contamination sits, undetected, until the moment it causes real, measurable harm — a denied mortgage application, a rejected auto loan, a collection call that makes no sense.
CTA #2: Check for Fragmented File Indicators
Use the ScorePivot Bureau Discrepancy Checker to scan for fragmented file indicators across all three major bureaus.
Run Bureau Discrepancy CheckSection 6: The Synthetic Dispute Pathway — How Fraudsters Weaponize the FCRA
Synthetic identity fraudsters exploit the Fair Credit Reporting Act's dispute process through "credit washing" — mass-filing dispute letters to force bureaus to delete negative items before they can be verified, exploiting the 30-day investigation window. The CPN (Credit Profile Number) scam, which sells fabricated 9-digit numbers as "legal alternatives" to SSNs, constitutes federal fraud under 18 USC 1028 (Identity Fraud), 1343 (Wire Fraud), and 1344 (Bank Fraud). The 2026 FCRA updates now require dispute specificity, higher furnisher verification standards, and documentation requirements designed to combat this abuse.
The Fair Credit Reporting Act is one of the most important consumer protection statutes in American law. It gives every consumer the right to dispute inaccurate information on their credit report. It requires credit bureaus to investigate those disputes within 30 days. It mandates that if a furnisher cannot verify the accuracy of the disputed data, the bureau must delete it. These are essential protections. And they are being systematically weaponized by fraud networks operating synthetic identities.
The technique is called "credit washing," and it exploits the structural mechanics of the dispute process. After a synthetic identity executes a bust-out and the derogatory accounts appear on the file, the fraud operation does not simply abandon the identity. In many cases, it files disputes — dozens, sometimes hundreds of dispute letters, submitted to all three bureaus, challenging every derogatory item on the file. If the furnisher cannot verify the account within 30 days, the bureau must delete it. The derogatory item disappears. The credit is washed clean.
WARNING: The CPN Scam Is Federal Fraud
A CPN — Credit Profile Number, Credit Privacy Number, Credit Protection Number — is a nine-digit number that scammers sell to consumers as a "legal alternative" to their Social Security number. It is not legal. There is no law authorizing the use of a CPN. The numbers sold as CPNs are typically stolen Social Security numbers — belonging to children, elderly individuals, incarcerated persons, or deceased individuals.
Using a CPN to apply for credit constitutes multiple federal crimes: 18 USC 1028 (Fraud and Related Activity in Connection with Identification Documents), 18 USC 1343 (Wire Fraud), 18 USC 1344 (Bank Fraud). Penalties include up to 30 years in federal prison.
The 2026 FCRA updates have introduced reforms designed to combat the weaponization of the dispute process. Under the new rules, disputes now require specificity: the consumer must identify the exact data that is incorrect, state why it is incorrect, provide supporting facts, and include relevant documentation. Generic form letters — "this is not mine" — without supporting detail may not trigger the same investigation obligations. Furnishers face higher verification standards: they must now provide documentation and evidence to support their verification, not simply respond "verified" without proof.
Section 7: The IRS Contamination Vector — When Tax Identity Meets Credit Identity
Synthetic identities do not only exist in credit files — they contaminate IRS records by filing fraudulent tax returns, claiming refunds, creating fake W-2s, and generating fabricated 1099s using real SSNs. The IRS 2026 Dirty Dozen includes AI-enabled IRS impersonation and identity theft involving IRS online account access. Victims may discover contamination only when their legitimate tax return is rejected because "a return has already been filed with this SSN," triggering delays of 120 to 180 or more days for resolution through the IRS Identity Theft Victim Assistance Program.
Most people think of synthetic identity fraud as a credit problem. It is. But it is also a tax problem, an employment problem, a benefits problem, and a government identity problem. The same SSN that anchors a synthetic identity in the credit bureau system can simultaneously be used to file tax returns, claim refunds, generate employment records, and access government services.
The mechanism is straightforward. A synthetic identity — or the fraud network operating it �� files a tax return using the real SSN. The return may claim a fabricated income from a nonexistent employer, generating a fake W-2. It may claim earned income credits, child tax credits, or other refundable credits. The IRS processes the return — typically early in the filing season — and issues a refund. When the real consumer files their legitimate return weeks or months later, the IRS rejects it. "A return has already been filed with this Social Security number."
The IRS IP PIN: Your First Line of Defense
The IRS Identity Protection PIN (IP PIN) is a six-digit number assigned annually that must be included on any tax return filed with your SSN. Without the correct IP PIN, no return can be filed — not by you, and not by a synthetic. The IRS expanded the IP PIN program to all taxpayers in 2021, and enrollment is free through irs.gov/ippin. This single step — obtaining an IP PIN — is the most effective defense against tax-related synthetic identity fraud.
Get Your IRS IP PINCTA #3: Check Your IRS Status NOW
Do not wait until tax season to discover the damage. Check your IRS status with the ScorePivot IRS Contamination Alert Tool.
Run IRS Contamination CheckSection 8: The Invisible Victim — Why You Will Not Know Until It Is Too Late
The defining characteristic of synthetic identity fraud is the absence of immediate victim notification — no alert, no notification, and no visible sign on your credit report until the damage has already been done. Warning signs include pre-approved credit offers for unfamiliar names arriving at your address, IRS notices about income you did not earn, collection calls for accounts you never opened, and credit applications denied despite strong history. Children are the most vulnerable targets because their SSNs can be exploited for 15 to 18 years before detection.
There is a moment in every synthetic identity fraud case when the real victim discovers what has happened. It is never early. It is never convenient. It is never gentle. It is a mortgage application denied three weeks before closing. It is a collection call at dinner for an account that makes no sense. It is a tax return rejected in April when you need the refund by May. The moment arrives like a sucker punch — sudden, disorienting, and deeply personal. And by the time it arrives, the person who caused it has already ceased to exist.
This is the cruelty at the center of synthetic identity fraud. Traditional identity theft is traumatic, but it is at least visible. Your credit card is used at a store you have never visited. Your bank account shows a withdrawal you did not make. There is a signal. An anomaly. Synthetic identity fraud produces no such signal. The synthetic identity lives in a parallel file. Its accounts do not appear on your credit report. Its payments do not affect your score. The two files — yours and the ghost's — exist in the same database, linked by the same SSN, but separated by different identifying data. You cannot see what you cannot access.
Subtle Warning Signs Most People Miss
- Pre-approved credit card offers arriving at your address but addressed to a name you do not recognize. Most people throw them away as junk mail.
- IRS notices about income you did not earn. Most people assume it was a clerical error. But that income was reported by a synthetic identity using your SSN.
- Collection calls for accounts you never opened. You tell the collector they have the wrong person and hang up. But they have the right SSN.
- Credit denials despite strong history. The denial letter cites metrics that do not match your actual profile. The lender's system pulled the synthetic's file.
Children represent the most acute vulnerability in the synthetic identity ecosystem. A child's SSN is uniquely attractive to fraud networks for reasons that are mathematically precise. A child has no credit history, which means there is no existing file for the bureau's matching algorithm to conflict with. A child is not monitoring their credit — indeed, a child does not even know they have a credit file. A child's SSN can be harvested and used to anchor a synthetic identity that operates undetected for fifteen to eighteen years.
The cruelest feature of synthetic identity fraud is the silence. There is no notification. No alert. No warning shot. There is only the moment you discover the wreckage — and by then, the person who caused it has already ceased to exist.
Section 9: The Platform Intelligence Report — What Reddit, TikTok, Facebook, and X Are Saying
Social media platforms serve as both vectors for synthetic identity fraud and early warning systems where victims first discover their compromised data. Reddit's r/personalfinance and r/IdentityTheft communities document users reporting mysterious second credit files and SSN matches to unknown names. TikTok hosts deepfake financial scams and CPN scheme promotion. Facebook AI-generated personas enable romance scams funneling to identity theft. X (Twitter) features security researcher threads on DPRK synthetic identity operations and real-time breach notifications.
Reddit: r/personalfinance, r/IdentityTheft, r/CRedit
The posts are remarkably consistent in their confusion: "I pulled my credit report and found a second file with my SSN but a completely different name. How is this possible?" "Someone opened accounts with my Social Security number but a different name and date of birth — what do I do?" "My 16-year-old tried to open a bank account and was told their SSN is already associated with a credit file."
The term "synthetic identity" rarely appears in these threads. People describe the symptoms without knowing the disease.
TikTok: The Viral Fraud Ecosystem
The Graphika research unit documented 27 accounts impersonating a single individual — Jaden Smith — across TikTok and YouTube for bank fraud purposes in March 2026 alone. These accounts use AI-generated video that is virtually indistinguishable from authentic footage. Simultaneously, a thriving ecosystem of "credit repair" influencers promotes CPN schemes — selling the idea that you can legally replace your SSN. None of the videos mention that using a CPN is a federal crime carrying penalties of up to 30 years in prison.
Facebook: Romance Scams and Credit Starter Packages
AI-generated persona scams funnel directly into identity theft and synthetic identity construction. Romance scams — where AI-generated military personnel, doctors, or businesspeople build emotional relationships with victims over weeks or months, then request personal information including SSNs "for emergency purposes" — remain endemic. Private groups selling "credit starter packages" are often selling synthetic identity kits.
X (formerly Twitter): Real-Time Fraud Intelligence
Financial security professionals, identity verification researchers, and investigative journalists use X to share findings in real time. Threads on DPRK synthetic identity operations — including the ID.me suspension of 130+ wallets linked to North Korean operatives and the 200% increase in DPRK infiltration attempts — circulate among security professionals. An active community of consumer advocates provides peer-to-peer guidance on dispute processes.
Section 10: The 7-Bureau Freeze Protocol — Beyond Equifax, Experian, and TransUnion
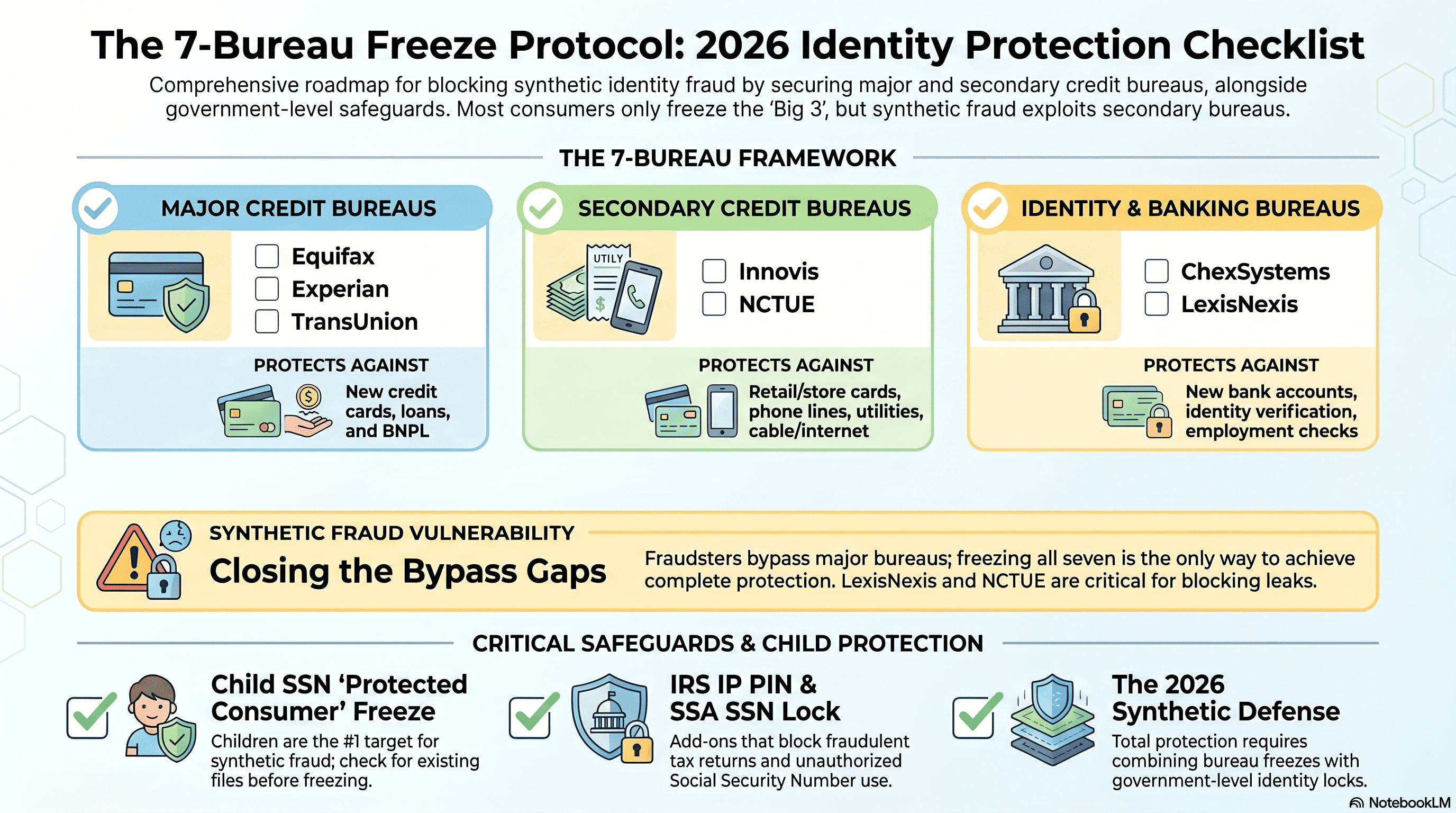
Infographic: The complete 7-bureau freeze protocol required to block synthetic identity fraud.
A comprehensive credit freeze requires freezing your file at seven consumer reporting agencies, not just the three major bureaus. The four lesser-known agencies — Innovis, NCTUE (National Consumer Telecom and Utilities Exchange), ChexSystems, and SageStream — are used by subprime lenders, auto dealers, phone carriers, utilities, banks, and specialty lending institutions. Freezing all seven is free under federal law and does not affect your credit score. Without a complete 7-bureau freeze, synthetic identities can still open utility accounts, bank accounts, and subprime credit lines using your SSN.
If you search the internet for "how to freeze your credit," you will find approximately ten thousand articles telling you to freeze your files at Equifax, Experian, and TransUnion. Those articles are not wrong. But they are incomplete. And in the context of synthetic identity fraud, incomplete protection is not protection at all. It is the illusion of protection — a locked front door while the back door, the side door, and the basement windows remain wide open.
Complete 7-Bureau Freeze Protocol
| Bureau | Website | Phone | Used By |
|---|---|---|---|
| 1. Equifax | equifax.com | (888) 298-0045 | Major lenders, mortgages, credit cards |
| 2. Experian | experian.com/freeze | (888) 397-3742 | Major lenders, mortgages, credit cards |
| 3. TransUnion | transunion.com/credit-freeze | (800) 916-8800 | Major lenders, mortgages, credit cards |
| 4. Innovis | innovis.com/securityFreeze | (800) 540-2505 | Subprime lenders, auto dealers, specialty finance |
| 5. NCTUE | nctue.com/consumer | (866) 349-5355 | Phone carriers, utilities, cable companies |
| 6. ChexSystems | chexsystems.com/security-freeze | (800) 428-2320 | 80% of US banks for checking/savings screening |
| 7. SageStream | sagestream.com | (888) 395-0277 | Specialty lenders, some consumer reporting |
Every one of these freezes is free. This is federal law. The Economic Growth, Regulatory Relief, and Consumer Protection Act of 2018 requires all consumer reporting agencies to offer free security freezes to all consumers. No charge to place the freeze. No charge to lift the freeze. A credit freeze does not affect your credit score. It does not close any existing accounts. It simply prevents new inquiries from pulling your file.
The 7-Bureau Freeze Protocol is the single most effective defensive measure available to any consumer against synthetic identity fraud. It takes approximately 60 to 90 minutes to complete all seven freezes. It costs nothing. And it eliminates the primary pathway by which synthetic identities seed new credit files using your SSN.
CTA #4: Track Your Freeze Status
Track your freeze status across all 7 bureaus with the ScorePivot 7-Bureau Freeze Status Dashboard. One screen. Complete visibility.
Open Freeze Status DashboardSection 11: The 2026 FCRA Updates — New Rules That Change Everything
The 2026 Fair Credit Reporting Act updates introduce mandatory 10-day preliminary investigations for high-risk errors, stricter furnisher verification standards requiring documentation (not just verbal confirmation), automatic classification of multi-bureau discrepancies as high-risk reporting errors, and new dispute specificity requirements. These changes shift the burden of proof from the consumer to the furnisher and create the strongest consumer protection framework in recent FCRA history, with particular benefits for synthetic identity fraud victims whose contaminated files create cross-bureau inconsistencies.
Change #1: 10-Day Preliminary Investigation for High-Risk Errors
Certain categories of errors — including accounts that appear on one bureau's report but not others, accounts with conflicting statuses across bureaus, and accounts flagged by FTC Identity Theft Reports — are now classified as high-risk. These items must receive a preliminary investigation within 10 days, not 30.
Change #2: Furnisher Documentation Requirements
Furnishers must now provide documentation and evidence to support their verification. If the furnisher asserts that the account is accurate, they must produce records demonstrating how the account was opened and what identity verification was performed. If they cannot produce this documentation, the bureau must delete the item. The burden of proof has shifted from the consumer to the furnisher.
Change #3: Multi-Bureau Discrepancies = High-Risk
If your Equifax report shows an account as "open" while TransUnion shows it "in collections" and Experian doesn't show it at all, such discrepancies are now automatically classified as high-risk errors. For synthetic fraud victims, this is significant because fragmented files almost always create multi-bureau discrepancies.
Change #4: Dispute Specificity Requirements
Disputes now require specific information: the exact data that is incorrect, why it is incorrect, what the correct data should be, and supporting documentation. For legitimate victims, this is beneficial — it forces the bureau to engage with the specific nature of the contamination rather than processing through a generic workflow.
Section 12: Predictive Scoring and the New Credit Architecture — FICO 10T, VantageScore 4plus, UltraFICO
New credit scoring models are making synthetic identity fraud harder to sustain. FICO 10T uses trended data analyzing 24+ months of payment behavior patterns, making it better at detecting the sudden credit buildup characteristic of synthetic incubation. VantageScore 4plus incorporates consumer-permissioned open banking data, providing up to 10% predictive lift, and uses real bank account behavior that is significantly harder for synthetics to fabricate. Both models are now being adopted by Fannie Mae and Freddie Mac following an April 2026 FHFA announcement.
The credit scoring models that have governed lending decisions for the past two decades were built for a world that no longer exists. Classic FICO looks at a snapshot — your credit profile at a single point in time. A synthetic identity, by definition, is engineered to look good on a snapshot. On-time payments. Low utilization. The model tells you it's a responsible borrower. The model is wrong.
FICO 10T introduces trended data into the scoring model. Instead of looking at a single snapshot, FICO 10T examines 24+ months of payment behavior patterns. It tracks the trajectory of your credit usage over time — are your balances increasing or decreasing? Are you paying more or less than the minimum? This temporal analysis is particularly effective at detecting synthetic identity incubation patterns.
VantageScore 4plus combines traditional credit bureau data with consumer-permissioned open banking data. The consumer can permission access to their bank account data — checking and savings account balances, transaction patterns, income deposits, bill payment history. For synthetic identity detection, the significance is this: bank account behavior is dramatically harder to fabricate than credit tradeline behavior.
On April 22, 2026, the Federal Housing Finance Agency (FHFA) announced next steps for the adoption of both VantageScore 4.0 and FICO 10T by Fannie Mae and Freddie Mac. This marks a fundamental shift in how creditworthiness is assessed.
Section 13: The Detection Framework — How to Know If a Synthetic Is Attached to Your File
Detecting synthetic identity contamination requires a systematic, multi-source review process that extends beyond simply checking your credit report. The ScorePivot 10-step detection checklist includes pulling reports from all three major bureaus and comparing them for discrepancies, checking for unknown addresses and inquiries, reviewing SSA earnings records for phantom employment, verifying IRS transcripts for unauthorized filings, checking ChexSystems for unknown bank accounts, and reviewing NCTUE for unauthorized utility and telecom accounts.
The ScorePivot 10-Step Synthetic Identity Detection Checklist
- 1Pull credit reports from ALL THREE major bureaus simultaneously. Go to AnnualCreditReport.com. Pull Equifax, Experian, and TransUnion on the same day. Look for discrepancies between them.
- 2Check for unknown addresses, phone numbers, or employer names. Review the "personal information" section of each report carefully.
- 3Look for accounts you do not recognize. Pay particular attention to recently opened thin tradelines with short histories and low limits.
- 4Check for inquiries from lenders you never applied to. Hard inquiries should correspond to applications you actually submitted.
- 5Review authorized user accounts. If you are listed as an authorized user on an account you did not authorize, this may indicate piggybacking.
- 6Check your SSA earnings record. Go to ssa.gov and review your earnings record for wages from employers you never worked for.
- 7Verify IRS transcripts. Access your IRS account at irs.gov/account. Verify that every return filed under your SSN was filed by you.
- 8Check ChexSystems. Request your ChexSystems consumer report at chexsystems.com for bank accounts you did not open.
- 9Review NCTUE. Request your NCTUE consumer report at nctue.com/consumer for utility and telecom accounts you did not open.
- 10Set up fraud alerts. An initial fraud alert is free and lasts one year. Extended fraud alert lasts seven years for confirmed identity theft victims.
CTA #5: Run the Full Synthetic Identity Risk Scan
The ScorePivot Synthetic Identity Risk Scanner checks for 47 indicators of synthetic contamination across credit, tax, banking, and utility records. Start your free scan now.
Run Your Free ScanIndependent review. We may earn a referral, but your price stays the same.
Section 14: The Dispute Playbook — Metro 2 Compliance and the New Verification Standards
Under the 2026 FCRA rules, effective dispute filings for synthetic identity fraud contamination must be specific, documented, and filed simultaneously with all three major bureaus. The dispute must identify the exact fraudulent account, state that it was opened by a synthetic identity, include an FTC Identity Theft Report and police report, and specify the incorrect data with supporting documentation. Metro 2, the standardized credit reporting format, includes specific status codes that are critical for victims to understand.
The 10-Step Dispute Protocol for Synthetic Identity Contamination
- Step 1: Document everything before you file. Take screenshots of every questionable item.
- Step 2: File an FTC Identity Theft Report at IdentityTheft.gov. This generates the official report that unlocks your FCRA Section 605B rights.
- Step 3: File a police report with local law enforcement, specifying "synthetic identity fraud using my Social Security number."
- Step 4: File disputes with ALL THREE bureaus simultaneously. Do not file with just one.
- Step 5: Be SPECIFIC in your dispute. For each disputed item, state the exact account, what is wrong, why it is wrong, and what the correct information should be.
- Step 6: Include IRS Form 14039 if tax records are affected.
- Step 7: Invoke the high-risk error classification if your items show multi-bureau discrepancies.
- Step 8: If the furnisher cannot produce origination documentation within the investigation window, the bureau MUST delete the item.
- Step 9: Maintain a paper trail. Use certified mail with return receipt for all correspondence.
- Step 10: If the bureau fails to investigate properly, escalate to the CFPB at consumerfinance.gov.
Key Metro 2 Status Codes for Synthetic Fraud Disputes
| Code | Meaning | Relevance |
|---|---|---|
| XB | Account reported as fraud / identity theft | Target status for synthetic fraud accounts |
| DF | Account disputed by consumer under FCRA | Should appear during active dispute |
| XH | Fraud investigation pending | Account under fraud review |
| 97 | Account transferred or sold | Common after bust-out, account sold to collector |
Section 15: The IRS Defense Stack — IP PINs, Identity Theft Affidavits, and Tax Account Monitoring
The IRS defense stack against synthetic identity contamination includes five critical components: obtaining an Identity Protection PIN (IP PIN) at irs.gov/ippin, filing Form 14039 (Identity Theft Affidavit) if contamination is suspected, creating an IRS Online Account for ongoing monitoring, requesting IRS tax transcripts to verify all filings, and registering at SSA.gov to monitor earnings records for phantom employment. The IP PIN is the single most effective defense against tax-related synthetic fraud.
Layer 1: Get an IRS Identity Protection PIN (IP PIN) IMMEDIATELY
This is the single most important step in this entire document. The IP PIN is a six-digit number assigned by the IRS that must be included on any tax return filed with your SSN. If someone attempts to file a return using your SSN without the correct IP PIN, the return will be rejected. Enrollment is free through irs.gov/ippin and takes approximately 15 minutes.
Layer 2: File Form 14039 if You Suspect Contamination
If your detection process revealed any indication that your SSN has been used for unauthorized tax filings, file Form 14039 with the IRS. This initiates the Identity Theft Victim Assistance Program. Resolution timelines typically take 120 to 180 days or more.
Layer 3: Create an IRS Online Account
Go to irs.gov/account. This provides access to filed returns, payment history, balance information, and estimated tax payments. Monitor this account at minimum quarterly.
Layer 4: Request IRS Tax Transcripts
Request a "Return Transcript," "Account Transcript," and "Wage and Income Transcript." Review each carefully for W-2s from employers you have never worked for or 1099s for income you never received.
Layer 5: Register at SSA.gov and Monitor Earnings
Create your "my Social Security" account and review your earnings statement. Compare it to your actual employment history. If you see wages from employers you have never worked for, contact the SSA immediately.
CTA #6: Layer Your IRS Defense
Use the ScorePivot IRS Contamination Alert Tool — monitors for unauthorized filings, transcript anomalies, and employment record discrepancies.
Run IRS Defense CheckSection 16: The Credit Rehabilitation Roadmap — Rebuilding After Synthetic Contamination
Credit rehabilitation after synthetic identity fraud follows a five-phase process spanning approximately two years: Triage (Days 1-30) focuses on freezing all seven bureaus, filing disputes, and securing government accounts. Stabilization (Days 31-90) involves following up on disputes and monitoring for new fraudulent accounts. Reconstruction (Days 91-180) begins rebuilding with secured credit products and credit-builder loans. Acceleration (Days 181-365) graduates to unsecured products. Monitoring (Year 2+) establishes ongoing review cadences.
Phase 1: Triage (Days 1-30)
Freeze all seven bureaus. File disputes with all three major bureaus. File police report and FTC Identity Theft Report. File IRS Form 14039 if affected. Obtain IRS IP PIN. Document everything. Notify banks and credit card issuers. Change all passwords. Enable two-factor authentication. Begin monitoring.
Phase 2: Stabilization (Days 31-90)
Follow up on all disputes. Check status with each bureau. If items were verified despite being fraudulent, prepare re-disputes with additional documentation. Monitor all three credit reports weekly. Verify all seven freezes are active. Consider consulting a consumer rights attorney if disputes are not producing results.
Phase 3: Reconstruction (Days 91-180)
Apply for a secured credit card. Consider a credit-builder loan. Ask to be added as a legitimate authorized user on a trusted family member's account. Enroll in rent reporting services. Keep utilization below 10%. Make every payment on time, without exception.
Phase 4: Acceleration (Days 181-365)
Apply for an unsecured credit card. Diversify your credit mix by adding a different type of credit product if you can do so responsibly. Continue maintaining 100% on-time payment history. Keep utilization below 10%. Do not close old accounts. Limit new applications to one or two per quarter.
Phase 5: Monitoring (Year 2 and Beyond)
Monitor credit reports at minimum monthly. Review IRS transcripts annually. Check SSA earnings record annually. Verify all seven freezes are active quarterly. Review ChexSystems and NCTUE reports annually. Stay informed about new fraud trends.
Section 17: The 90-Day Synthetic Identity Defense Protocol
The 90-Day Synthetic Identity Defense Protocol is a structured, week-by-week action plan that takes any consumer from unprotected to fully defended in three months. Week 1 focuses on pulling reports, freezing all seven bureaus, and securing IRS and SSA accounts. Weeks 2-4 cover dispute filing, fraud alerts, account security, and monitoring setup. Month 2 addresses dispute follow-up, data broker removal, and digital footprint auditing. Month 3 verifies resolution, confirms clean reports, and establishes ongoing monitoring cadences.
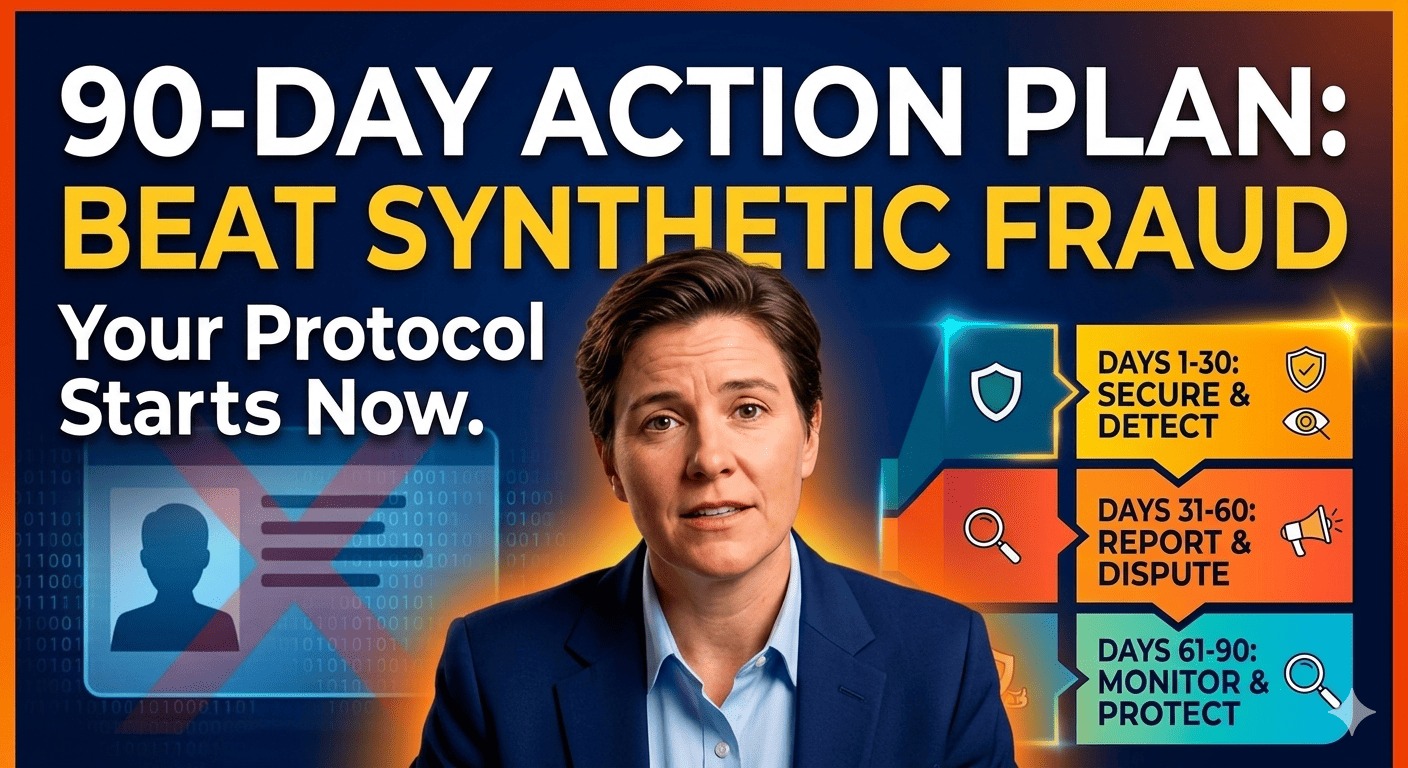
Week 1: Foundation
- Day 1: Pull your credit reports from all three major bureaus at AnnualCreditReport.com. Save or print all three reports.
- Day 1-2: Compare all three reports side by side. Document any discrepancies, unknown accounts, unfamiliar addresses, phantom inquiries.
- Day 2-3: Freeze your credit at all seven bureaus: Equifax, Experian, TransUnion, Innovis, NCTUE, ChexSystems, and SageStream.
- Day 3-4: Create or log into your SSA.gov account. Review your earnings record for phantom employment.
- Day 4-5: Create or log into your IRS Online Account. Request tax transcripts and review for unauthorized filings.
- Day 5: Enroll in the IRS Identity Protection PIN program at irs.gov/ippin.
- Day 6-7: Request your ChexSystems report and NCTUE report. Review for unauthorized accounts.
Weeks 2-4: Dispute and Secure
- Week 2: File disputes with all three bureaus. File FTC Identity Theft Report. File police report. Set up fraud alerts. File IRS Form 14039 if needed.
- Week 2: Register for free credit monitoring. Set up account alerts on all financial accounts.
- Week 3: Enable two-factor authentication on all financial accounts, email, and government accounts. Change passwords. Use unique, strong passwords.
- Week 4: Review all authorized user relationships. Remove yourself from unauthorized accounts. Verify existing accounts for unauthorized changes.
Month 2: Follow-Up and Fortify
- Weeks 5-6: Follow up on all disputes. If items were "verified" despite being fraudulent, prepare re-disputes with additional documentation.
- Weeks 6-7: Verify all seven freezes are active.
- Weeks 7-8: Begin data broker removal process. Opt out individually or use a service like DeleteMe.
- Week 8: Audit your digital footprint. Remove sensitive data that is unnecessarily public.
Month 3: Verify and Maintain
- Weeks 9-10: Pull updated credit reports from all three bureaus. Verify all disputed fraudulent items have been removed. If any remain, escalate.
- Weeks 10-11: Confirm clean reports from all three bureaus. Verify no new fraudulent accounts have appeared. Review IRS and SSA accounts again.
- Weeks 11-12: Establish ongoing monitoring cadence: weekly credit check, monthly IRS review, quarterly freeze verification, annual SSA review.
At the end of 90 days, you will have: frozen all seven bureaus, disputed all identified fraudulent items, secured your IRS and SSA accounts, removed your data from major brokers, hardened all financial accounts with strong authentication, and established an ongoing monitoring practice that will detect new threats quickly. You will have moved from unprotected to defended.
CTA #7: Track Your 90-Day Protocol Progress
Track every step of your 90-Day Defense Protocol with the ScorePivot 7-Bureau Freeze Status Dashboard and Credit Rehabilitation Progress Tracker.
Open Progress TrackerSection 18: The ScorePivot Diagnostic Tool Suite — Your Real-Time Threat Assessment
ScorePivot offers five integrated diagnostic tools for synthetic identity fraud detection and defense: the Synthetic Identity Risk Scanner (47 contamination indicators), the Bureau Discrepancy Checker (cross-bureau data comparison), the 7-Bureau Freeze Status Dashboard (single-screen freeze monitoring), the IRS Contamination Alert Tool (unauthorized filing monitoring), and the Credit Rehabilitation Progress Tracker (5-phase recovery milestone tracking). These tools provide the centralized visibility that the fragmented credit reporting system was never designed to offer.
1. Synthetic Identity Risk Scanner
Analyzes credit report data for 47 distinct indicators of synthetic identity contamination: file fragmentation indicators, account anomaly indicators, identity inconsistency indicators, and behavioral pattern indicators.
2. Bureau Discrepancy Checker
Automates cross-bureau comparison. Cross-references every data point: account names, balances, statuses, addresses, inquiries. Any discrepancy is flagged and linked to the specific FCRA dispute pathway.
3. 7-Bureau Freeze Status Dashboard
Provides a single screen showing freeze status at all seven agencies. Green = frozen. Red = unfrozen. Yellow = verification needed. One screen. Complete visibility.
4. IRS Contamination Alert Tool
Monitors for unauthorized returns filed under your SSN, transcript anomalies, and employment record discrepancies between IRS records and SSA earnings.
5. Credit Rehabilitation Progress Tracker
Maps your recovery against the 5-phase rehabilitation roadmap. Tracks milestone completion — freezes placed, disputes filed, disputes resolved, accounts opened, payment history streaks, utilization targets met.
These five tools are designed to work together as an integrated suite. The Risk Scanner identifies the threat. The Discrepancy Checker pinpoints the evidence. The Freeze Dashboard confirms the defenses. The IRS Alert monitors the tax dimension. And the Progress Tracker guides the recovery.
Section 19: The Affiliate Arsenal — Tools, Services, and Monitoring Platforms That Actually Work
The most effective identity protection strategy combines ScorePivot's diagnostic tools with specialized third-party services. Key recommendations include: IdentityIQ for comprehensive 3-bureau monitoring, Aura for all-in-one family protection, NordProtect for dark web SSN surveillance, Credit Repair Cloud for operators building identity theft remediation services, and Client Dispute Manager for Section 605B blocking letters and dispute templates.
IdentityIQ — Best for 3-Bureau Monitoring
Detecting fragmented file contamination requires seeing the complete file across all three bureaus simultaneously — not just the scored report. IdentityIQ's full 3-bureau pull reveals the personal information section, the alias section, and every associated address — the exact places where synthetic identity contamination hides.
Get Your 3-Bureau Report ($1 Trial)Independent review. We may earn a referral, but your price stays the same.
Aura — Best All-in-One Platform
Aura combines identity monitoring, credit monitoring, antivirus protection, VPN, password management, and parental controls into a single subscription. For families — particularly families with children whose SSNs are vulnerable — Aura's family plan provides coverage for every member of the household. Monitors all three bureaus daily and alerts you the moment a new alias, inquiry, address, or account appears.
Try Aura All-in-One ProtectionIndependent review. We may earn a referral, but your price stays the same.
NordProtect — Best for Dark Web SSN Surveillance
The moment a fraudster purchases your SSN on the dark web, they have 12-24 months before the consumer typically discovers the fraud. NordProtect's dark web scan detects your SSN in marketplace listings before the synthetic identity is constructed — giving you the opportunity to freeze, lock, and notify authorities before credit damage begins.
Scan the Dark Web for Your SSNIndependent review. We may earn a referral, but your price stays the same.
Credit Repair Cloud — For Operators Building Premium Services
Synthetic identity remediation is the credit repair industry's highest-value, highest-margin service. The Credit Hero Challenge teaches operators how to build a compliant credit repair business that can help victims of synthetic identity fraud through the complex Section 605B dispute process.
Start the Credit Hero ChallengeIndependent review. We may earn a referral, but your price stays the same.
Client Dispute Manager — Best for Section 605B Letters
Removing synthetic identity contamination from your credit file requires Section 605B blocking letters — not standard credit disputes. CDM's professionally formatted 605B letters include the precise statutory citation that each bureau's compliance department must respond to.
Get Section 605B Letter TemplatesIndependent review. We may earn a referral, but your price stays the same.
AFFILIATE DISCLOSURE: ScorePivot may earn a commission through affiliate links in this section. This does not affect our editorial independence, recommendations, or the price you pay. We only recommend products we have independently evaluated. All pricing information is approximate and subject to change.
Section 20: The Final Word — You Are Not Powerless
Despite the scale and sophistication of the synthetic identity fraud crisis, individual consumers have effective defensive tools: freezing all seven credit bureaus is free and blocks new account creation, IRS IP PINs prevent unauthorized tax filings, the 2026 FCRA updates provide stronger dispute rights than ever before, and diagnostic tools can detect contamination early. The 90-Day Defense Protocol transforms awareness into action. You are not powerless.
You have just read approximately 15,000 words about a crime that most Americans have never heard of. You know things now that your neighbors do not know, that your colleagues do not know, that your family members do not know. You know that synthetic identity fraud grew eightfold in 2025 and represents 11% of all global fraud. You know that it is projected to contribute to $40 billion in losses. You know that it exploits the fundamental architecture of the American credit reporting system — and that the same nine-digit number you received at birth can be used to build a person who has never existed.
That knowledge may have generated fear. If it did, I will not apologize for it. The fear is proportional to the threat. The threat is real. The numbers are not exaggerated. This is the fastest-growing fraud on Earth, and it targets everyone with a Social Security number.
But fear without agency is paralysis. And paralysis is exactly what serves the fraud networks. Every day that you do not freeze your credit is a day that a synthetic can use your SSN to seed a file. Every year that you do not check your IRS transcripts is a year that an unauthorized return can be filed. Every month that you do not monitor your credit reports is a month that contamination can grow undetected.
So here is the pivot. Here is the part where the documentary becomes a manual. Here is where you stop watching and start acting.
You now have something that 99% of Americans do not have. You have awareness. You understand the threat — not in vague terms, but in operational detail. You know how synthetic identities are built, how they incubate, how they detonate, and how they contaminate. You know the six phases of the lifecycle. You know the seven bureaus. You know the ten detection steps. You know the five phases of rehabilitation. You know the 90-day protocol.
You have a protocol. The 90-Day Synthetic Identity Defense Protocol is a structured, day-by-day, week-by-week plan that requires no special tools, no professional assistance, and no financial investment beyond your time. It is free. It is comprehensive. It works.
You have tools. The ScorePivot diagnostic suite provides the centralized visibility that the fragmented credit reporting system was never designed to offer.
And you have rights. The 2026 FCRA updates have given you stronger dispute rights than any American consumer has ever had. The burden of proof has shifted from you to the furnisher. Multi-bureau discrepancies trigger automatic high-priority review. The system is not perfect. But it is better than it was. And it is most effective when used by consumers who understand how it works — consumers like you.
YOUR THREE ACTIONS — START NOW
FREEZE all 7 bureaus today
See the 7-Bureau Freeze Protocol →SCAN your credit files for synthetic contamination
Run Your Free Scan →MONITOR your IRS account for unauthorized filings
Get Your IRS IP PIN →You are not powerless. You are informed, equipped, and capable of defending yourself.
Start today. The protocol is in your hands. The tools are at your fingertips. And the person who might have built a ghost out of your data will find, when they try, that your defenses were already in place.
IMPORTANT DISCLAIMERS
The information provided in this article is for educational and informational purposes only. ScorePivot is not a credit repair organization, credit counseling service, or financial advisory firm. This content does not constitute legal, financial, tax, or credit repair advice. Individual situations vary. Consult qualified professionals — including attorneys, CPAs, and financial advisors — before making decisions based on this content. ScorePivot does not guarantee specific outcomes. All statistics cited are from publicly available sources and are believed accurate as of the publication date but may change. Affiliate relationships are disclosed throughout this article.
© 2026 ScorePivot. All rights reserved. | Published April 24, 2026